ACME Corporation (fictitious name) is a leading provider of cloud-based software solutions for small and medium-sized businesses. In 2021, the company experienced a cyber breach that exposed the personal data of millions of its customers. The breach occurred when a hacker gained access to ACME’s network by using an employee’s stolen credentials.
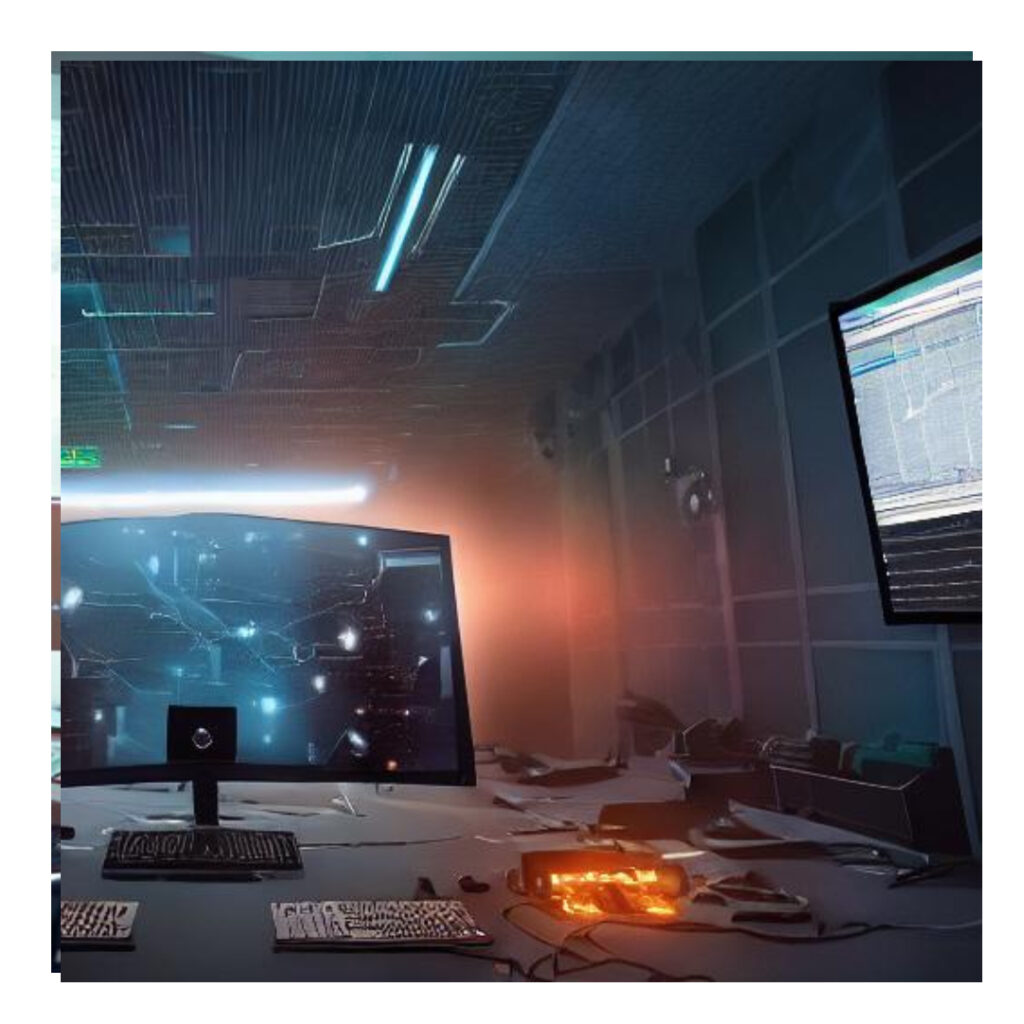
The hacker was able to go undetected for several months, during which time they exfiltrated a large amount of sensitive data. It wasn’t until ACME’s customers began reporting suspicious activity on their accounts that the company realized something was wrong. By then, it was too late. The damage had been done, and ACME’s reputation was severely damaged as a result.
Upon further investigation, it was discovered that the hacker had accessed the network using a compromised employee’s login credentials. This employee had fallen victim to a phishing attack and had unknowingly provided the hacker with access to the company’s network.
If ACME had been utilizing continuous log monitoring, the breach may have been prevented. Continuous log monitoring involves the continuous collection and analysis of log data from various systems and devices within a network. By analyzing this log data in real-time, security teams can detect anomalies and suspicious activity that may indicate a cyber attack.
In the case of ACME, continuous log monitoring would have alerted the security team to the fact that an unauthorized user was accessing the network using an employee’s credentials. The team could then have taken immediate action to investigate and stop the attack before it caused any harm.
Continuous log monitoring can also help organizations to comply with various regulations and standards, such as the General Data Protection Regulation (GDPR) and the Payment Card Industry Data Security Standard (PCI DSS). These regulations require companies to implement robust security measures to protect sensitive data, and continuous log monitoring is an essential component of a comprehensive security strategy.
The lesson learned is that ACME Corporation’s cyber breach could have been prevented with the use of continuous log monitoring. By continuously collecting and analyzing log data, security teams can detect and respond to potential threats in real-time, protecting the organization and its customers from harm. Investing in continuous log monitoring is not only essential for protecting against cyber attacks, but it also helps organizations to comply with industry regulations and standards.
